Preemptive Exposure ManagementBuilt For AI-Driven Attack Timelines.
AI-driven Preemptive Exposure Management for emerging threats. Validate exposure, mitigate autonomously at the edge, and leverage operational reach to outpace attackers who weaponize in a day – with the watchTowr Platform.
The watchTowr Platform is used in the world's most targeted industries.
Banking
Technology
Insurance
Telecoms
Government
Transport
Crypto
Fintech
Healthcare
Ecommerce
Mining
Gaming
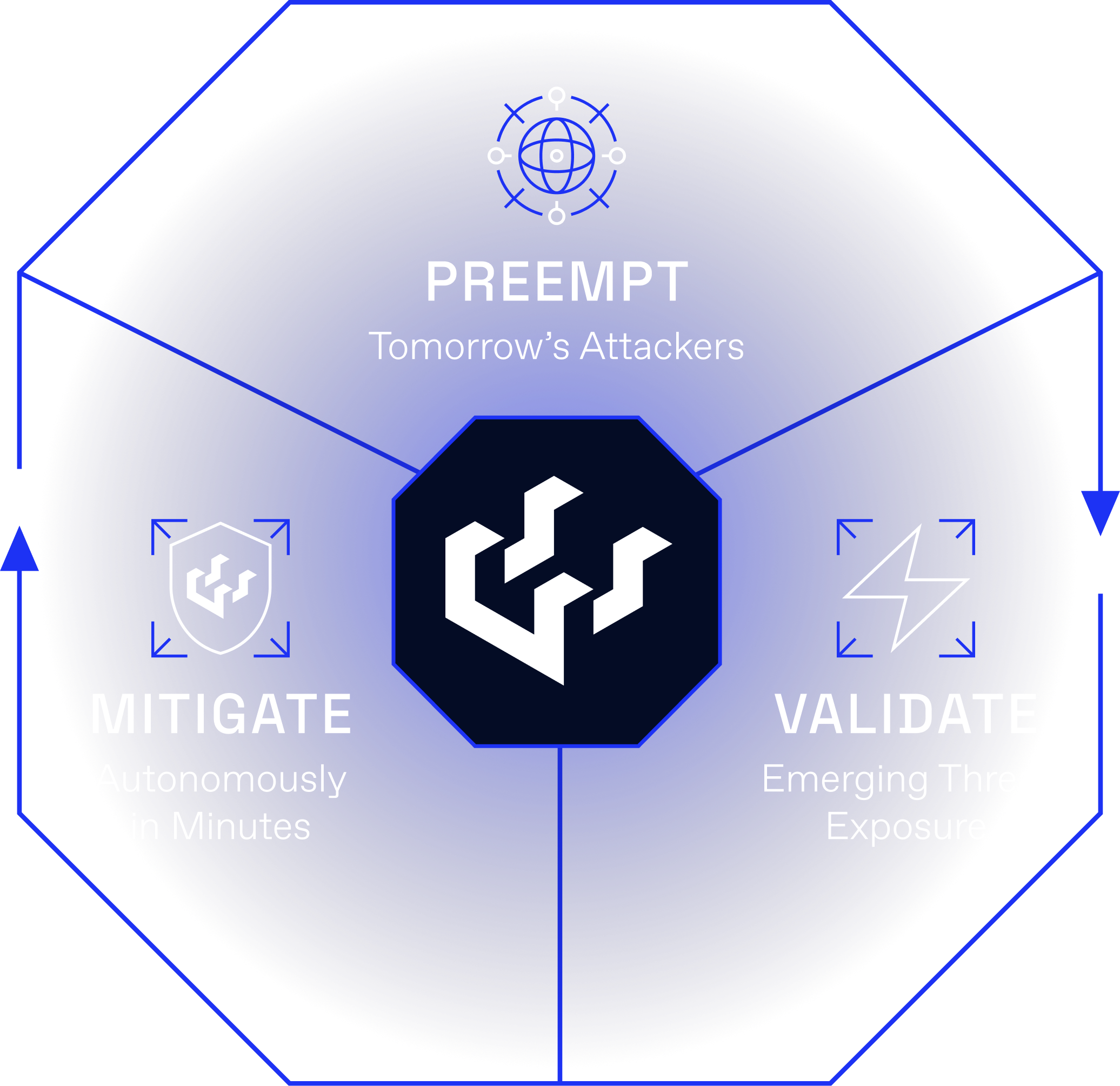
We Simulate Tomorrow's Attackers, Today.
The watchTowr Platform mirrors what real attackers do, continuously identifying and validating how your organization could be breached today at the same speed those attackers operate.
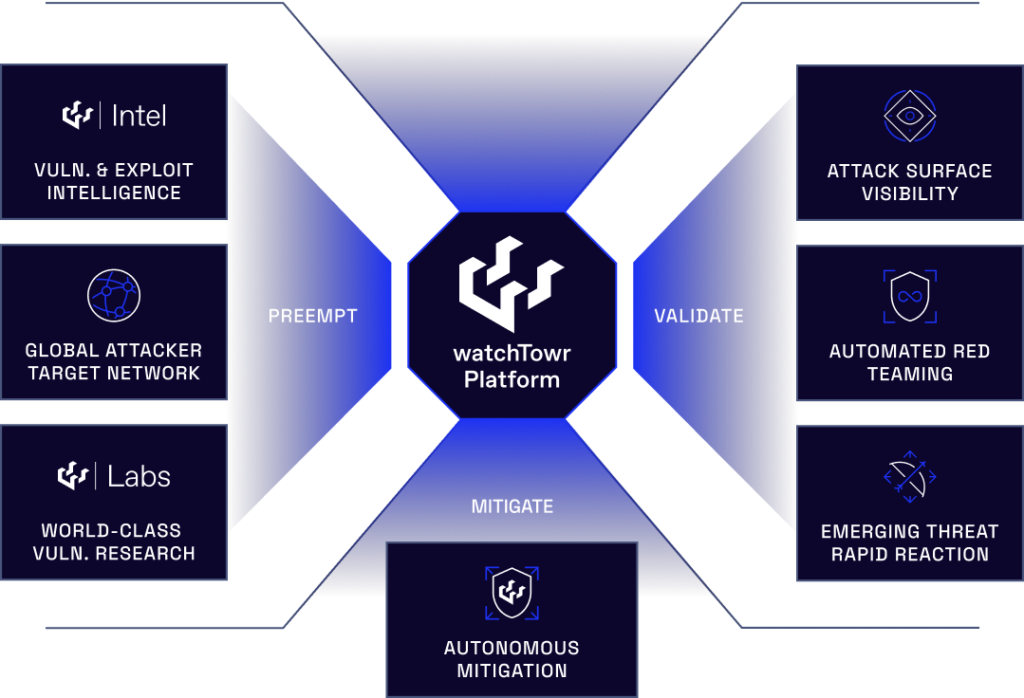
This Is Not Attack Surface Management.
This Is Not Threat Intelligence.
This Is Preemptive Exposure Management.
Real-Time Visibility
Continuous attacker-perspective discovery of your true external attack surface, including the unknown SaaS, subsidiaries, forgotten cloud assets, and shadow IT that attackers find first.
Cutting-Edge Tactics and Techniques
Validated against the same MITRE ATT&CK Initial Access tactics that real attackers use today, refreshed continuously as the threat landscape shifts beneath you.
Continuous Testing
Constant validation rather than point-in-time snapshots, because your exposure changes every day and your testing should match.
Rapid Reaction
AI-driven exposure identification within minutes of new threats emerging, with Active Defense pushing mitigation to the edge in hours rather than weeks.
Exploitation Now Moves Faster Than Remediation.
AI-enabled attackers analyze and weaponize published vulnerabilities within hours of disclosure. Enterprise patch cycles still take weeks. Rapid Reaction rapidly identifies and validates exposure to emerging threats, and Active Defense pushes autonomous mitigation to the edge while remediation is underway.
Attackers Now Weaponize In Hours
AI-enabled attackers analyze and weaponize disclosed vulnerabilities within hours of publication, often before the disclosing vendor's own customers are aware a patch exists.
KEV Catalogs Lag By Hundreds Of Days
Industry catalogs of known-exploited vulnerabilities lag actual exploitation by hundreds of days. By the time a CVE is added, it has been used in the wild for months.
Patch Cycles Still Take Months
Enterprise mean time to patch sits at 30 days or more, and has not structurally improved in a decade. Remediation cadence is human-paced and slow.
The Old Model Is Permanently Broken
The asymmetry is structural. It cannot be solved by patching faster, hiring more analysts, or buying another scanner. The response has to operate at attacker speed.
Deploy in Hours. Outpace Tomorrow's Threats Today.
Latest from watchTowr Labs and Intel
Preemptive Exposure Management gains momentum as organizations confront faster-moving threats SINGAPORE and LONDON and NEW YORK, June 02, 2026 (GLOBE
Every organization faces a fundamental question about its security posture: does it actually work? Not whether the right tools are
A Palo Alto PAN-OS buffer overflow vulnerability (CVE-2026-0300) has been disclosed, affecting the User-ID Authentication Portal (also known as the Captive Portal) on
Preemptive Exposure Management gains momentum as organizations confront faster-moving threats SINGAPORE and LONDON and NEW YORK, June 02, 2026 (GLOBE
Every organization faces a fundamental question about its security posture: does it actually work? Not whether the right tools are