watchTowr’s Continuous Assurance engine leverages the comprehensive tactics, techniques and vulnerabilities used by real-world attackers, today.
Continuously find exploitable and validated ways to compromise your attack surface, with the watchTowr Platform.
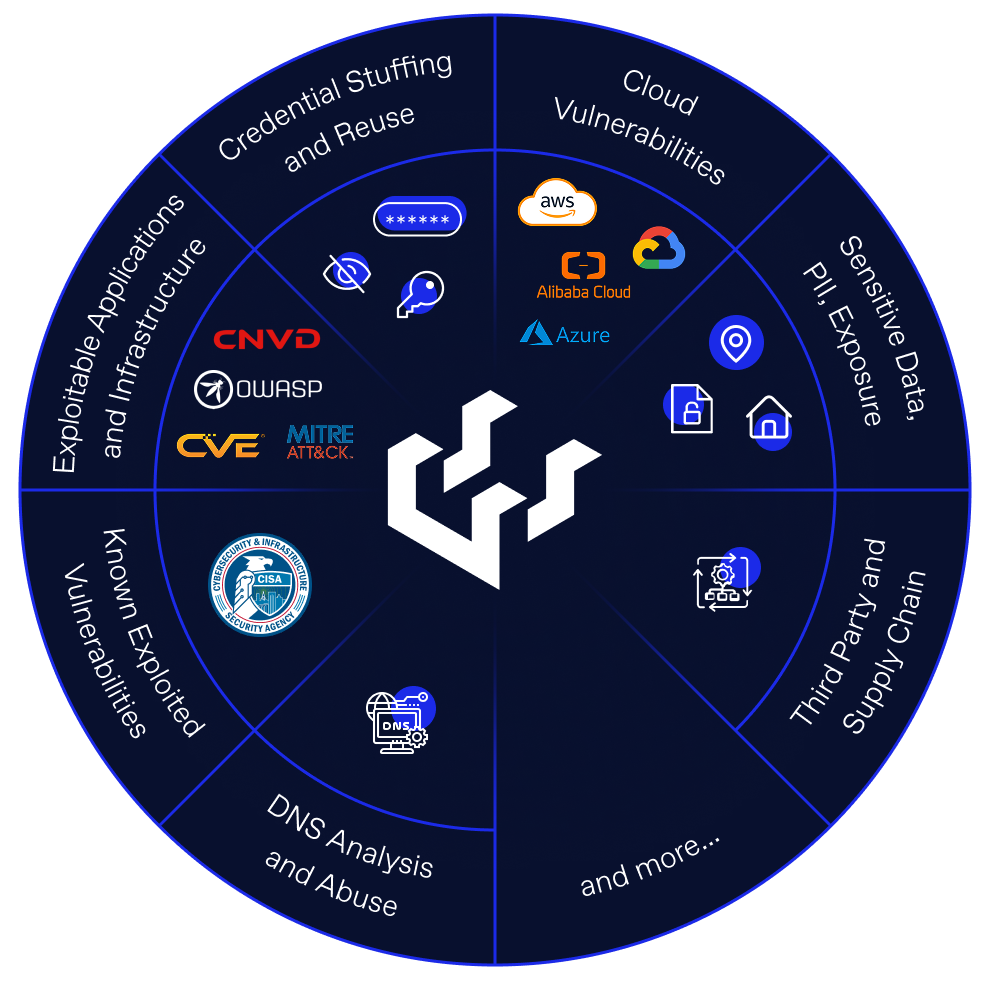
Mimicking the persistence of real-world attackers and ransomware gangs – the watchTowr Platform utilizes the full-spectrum of MITRE ATTACK Initial Access tactics and techniques.
Using data correlation, and tiered attribution confidence systems, the watchTowr Platform can automatically attribute assets to your organization with confidence – not requiring continual manual intervention.

watchTowr’s industry-leading Threat and Vulnerability Research capabilities fuel the watchTowr Platform’s Continuous Assurance engine.