watchTowr’s Automated Red Teaming engine validates exploitability across the full spectrum of MITRE ATT&CK Initial Access tactics, using the same techniques real-world attackers and ransomware gangs use today.
Continuously find exploitable and validated paths to compromise across your attack surface, with the watchTowr Platform.
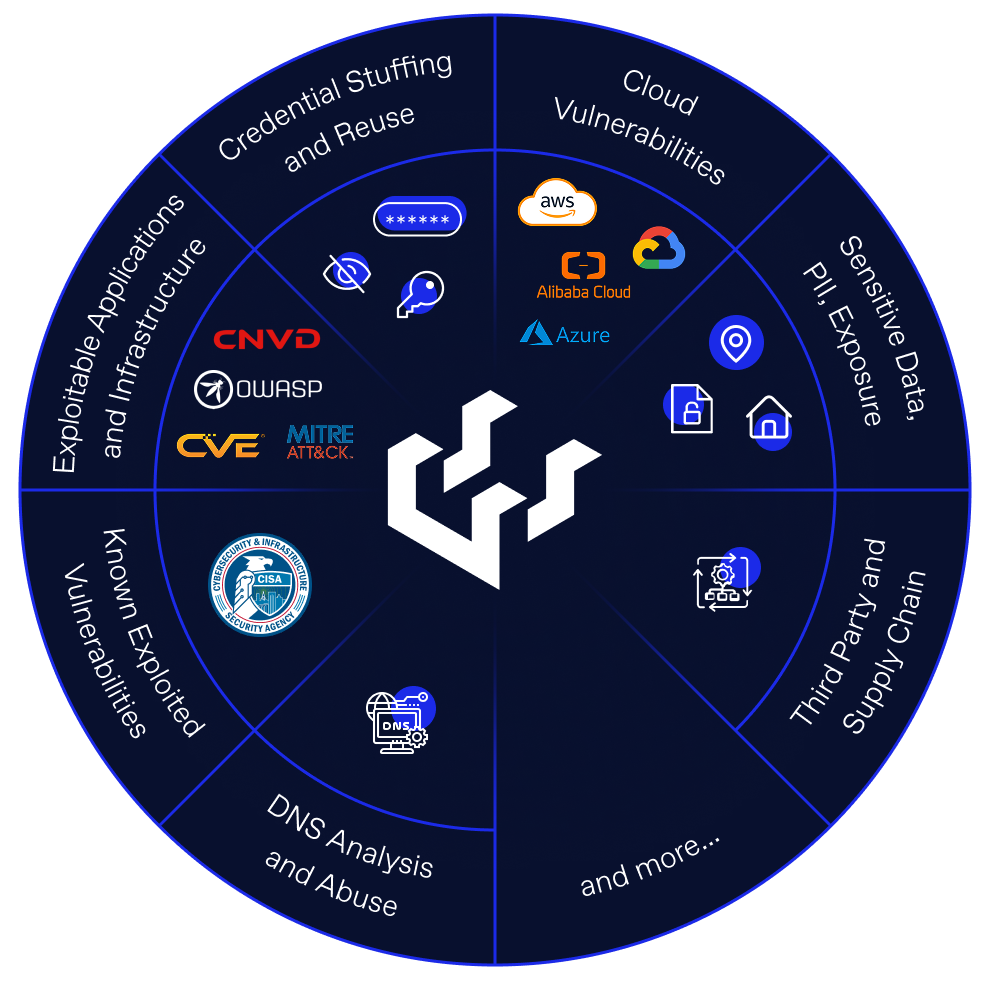
Mimicking the persistence of real-world attackers and ransomware gangs, the watchTowr Platform utilizes the full-spectrum of MITRE ATTACK Initial Access tactics and techniques.
As AI-enabled attackers generate novel tactics faster than traditional coverage updates can track, the Platform adapts continuously, drawing on real attacker telemetry rather than waiting for a periodic refresh cycle.
Using data correlation, and tiered attribution confidence systems, the watchTowr Platform can automatically attribute assets to your organization with confidence – not requiring continual manual intervention.

watchTowr’s industry-leading Threat and Vulnerability Research capabilities, combined with the real-world attacker telemetry of Attacker Eye and the prioritization signals of watchTowr Intel, fuel the watchTowr Platform’s Automated Red Teaming engine. Adversary Sight keeps the testing scope anchored to the real attack surface, and Rapid Reaction carries identified exposure into operational response.