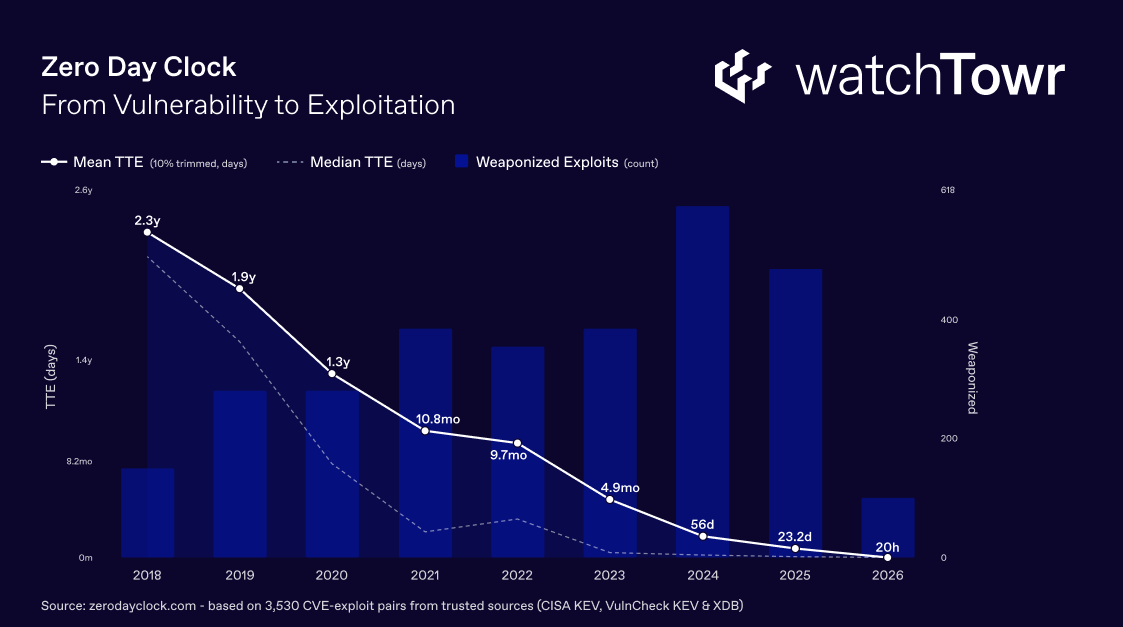
AI-driven exploitation has changed the equation for defenders. As an industry, we have spent the last several years watching the timeline between disclosure of a vulnerability, and observed in-the-wild exploitation aggressively compress, to the point that it has become a fairly predictable pattern.
We’ve watched our reality change – what once took weeks took days, what took days took hours, and every major vulnerability event reinforced the same uncomfortable trend: the window between disclosure and in-the-wild exploitation was shrinking, and defenders were steadily losing ground to time.
The data, including that from Zero Day Clock, confirms what many of us have felt for years. Exploitation timelines have not just compressed – they have collapsed:
AI has now accelerated this further, and dramatically so. Large language models and AI-driven tooling have demonstrably reduced the time required to:
- Analyze disclosed vulnerabilities
- Develop working exploits
- Weaponize weaknesses at scale
Capabilities that once demanded deep expertise and significant manual effort are now being augmented, accelerated, and in some cases fully automated – at scale.
Today, this is no longer a theoretical concern. Anthropic’s announcement of Claude Mythos Preview and Project Glasswing made the point with uncomfortable clarity: Mythos Preview found thousands of high-severity vulnerabilities, including some in every major operating system and web browser, with some of these vulnerabilities having survived decades of human review and millions of automated security tests. Given the rate of AI progress, it will not be long before such capabilities proliferate, potentially beyond actors who are committed to deploying them safely.
The implications for defenders are stark – if frontier AI models can autonomously discover and chain together vulnerabilities that human researchers missed for decades, the assumption that exploitation timelines will continue to compress is not pessimism but an inevitability that the industry now has to plan around.
The response from much of the industry, predictably, has been to tell organizations to patch faster – advice that, while well-intentioned, now has about as much strategic value as telling someone to be taller. To understand why, it helps to look at what patching actually involves in the environments that matter most.
The Laws of Enterprise IT Physics
Anyone who has worked inside an enterprise knows that patching is not a single action – it is a process governed by:
- Change windows
- Availability requirements
- Stability testing
- Dependency mapping
- Organizational sign-off
- Regulatory and compliance obligations
These constraints exist for good reason: they prevent outages, protect uptime, and ensure that fixes do not introduce new problems into production environments. They are also, critically, not going anywhere.
A hospital running a critical appliance cannot skip change control because a vulnerability was disclosed at 2am on a Saturday, and a financial institution managing thousands of endpoints cannot push untested patches into production because an exploit appeared on GitHub six hours after a CVE was assigned. Organizations operating in regulated industries – financial services, healthcare, critical infrastructure, government – face additional layers of compliance and audit requirements that make accelerating patch timelines even further a non-starter. The operational realities of enterprise IT have not changed, even as the threat landscape has accelerated dramatically around them – and expecting them to is not just unrealistic but infeasible.
This creates a gap, and it is growing. Exploitation timelines and remediation timelines are now on two fundamentally different trajectories – exploitation is increasingly measured in hours, while remediation in most enterprise environments is still measured in days or weeks. No amount of urgency will close that gap through patching alone, and the arrival of AI-driven exploitation capabilities has only widened it further.
The Shift: From Patching Speed to Mitigation Speed
So if patching alone cannot close the gap, the natural question becomes: what can?
At watchTowr, having focused on this problem for years – we confidently believe the realistic answer today is mitigation.
Not as a consolation prize or a temporary workaround that gets forgotten about, but as a primary, deliberate response capability that buys defenders the time they need to remediate vulnerabilities properly. If mitigation can fend off initial in-the-wild exploitation waves, defenders have bought themselves enough time to follow a safe, structured and responsible remediation process.
We’ve all seen the reality. When a critical vulnerability is disclosed and exploitation begins within hours, the organizations that typically survive without incident are not necessarily the ones that patched fastest – they are the ones that had the ability to:
- Identify their exposure immediately
- Mitigate exploitation at the network layer
- Patch in a safe and controlled manner while protected
In practice, this requires two things to happen very quickly:
- Organizations need to know whether they are affected – not in days or after a manual review, but in minutes – and,
- Organizations need the ability to block exploitation attempts while remediation is underway.
These two capabilities, executed at speed, are what convert a potential breach into a managed response at enterprise scale.
AI-Driven Exploitation Needs AI-Driven Rapid Reaction: Answering “Are We Affected?” in Minutes
This is the first half of the operational model that the watchTowr Platform was built around, and it reflects where watchTowr has always focused: getting organizations ahead of in-the-wild exploitation.
Every security team asks the same question when a new vulnerability hits: “Are we affected?” The challenge is that answering this question with confidence, across sprawling enterprise environments, has traditionally taken days – days that organizations no longer have.
AI-driven Rapid Reaction is the watchTowr Platform capability that closes this gap. Rather than relying on theoretical risk assessments or version-number guesswork, the watchTowr Platform identifies and validates exposure across client environments to provide trusted, high-fidelity answers.
Leveraging AI, our Rapid Reaction capabilities have reduced the time to determine an organization’s exposure across expansive attack surfaces to single-digit minutes in some cases.
When exploitation timelines are measured in hours, the speed of reaction changes the equation entirely. It is the difference between a security team responding from a position of control – knowing exactly what is affected, where it sits, and what to do about it – and a security team scrambling through a crisis with incomplete information.
For organizations in regulated industries where time-to-detection requirements are strict and audit trails matter, the ability to demonstrate rapid, validated identification of exposure is not just operationally valuable but a compliance imperative.
Active Defense: Mitigation at the Network Layer While Remediation Is Underway
Knowing exposure is only half of the problem – the other half is doing something about it before patches can be deployed. This is where Active Defense comes in.
Active Defense provides immediate, intelligence-driven mitigations at the network layer when exploitation is anticipated or already underway and patches do not yet exist, or cannot yet be deployed. These are:
- Ready-to-use, reviewable mitigation controls
- Informed by validated attacker behavior and confirmed exposure
- Opt-in and customer-controlled, with teams reviewing, testing, and applying mitigations in their own environment
- Designed to enable retesting to confirm mitigations are effective
Active Defense does not replace patching – it buys time for patching to happen properly, in a safe and controlled manner, without the panic of knowing exploitation is already underway. For organizations bound by the laws of Enterprise IT Physics – where change windows, stability requirements, and regulatory obligations mean that patching in minutes is simply not possible – Active Defense is the capability that bridges the gap between when exploitation begins and when remediation is complete.
AI-driven Rapid Reaction identifies the exposure, Active Defense enables mitigation immediately, and together they close the gap at the speed that the current threat landscape demands – allowing organizations to remediate from a position of control rather than a position of crisis.
The Trend Was Always There. AI-Driven Exploitation Lit the Fuse.
None of this is to suggest that AI created the problem. The compression of exploitation timelines has been a consistent, observable trend for years, with well-resourced threat actors, ransomware operators, and opportunistic attackers all moving faster with each passing quarter. The writing has been on the wall for a long time.
What AI has done, however, is remove any remaining ambiguity about whether the current model of vulnerability response is sustainable. It is not. When frontier AI models can autonomously discover zero-day vulnerabilities that survived decades of human review, the assumption that defenders can rely on patching speed alone becomes untenable – the organizations that continue down that path will find themselves consistently outpaced, while the organizations that invest in the ability to rapidly identify exposure and mitigate at speed will be the ones that avoid breaches.
Remediation and exploitation are now on two wildly different timelines, and the industry focus needs to shift from how quickly things will be exploited to how quickly organizations can mitigate, to buy teams the time for proper remediation.
This Is Preemptive Exposure Management
The watchTowr Platform combines Proactive Threat Intelligence and External Attack Surface Management to give organizations the ability to get ahead of in-the-wild exploitation – and it is already doing so, every day, for Fortune 500 companies and critical infrastructure providers globally.
AI-driven Rapid Reaction delivers trusted answers to “Are we affected?” within minutes of disclosure. Active Defense enables autonomous mitigation at the network layer while remediation is underway. Together, they fight AI-driven exploitation with AI-driven defense – at the same pace as the threat, giving security teams the one thing they need most: time to respond.
The watchTowr Platform was built for exactly this moment. The organizations already using it did not have to read this blog post to know that exploitation timelines were compressing – they experienced it, and they were already ahead.
When exploitation happens in hours, watchTowr delivers what no one else can: time to respond.
If you want to see how watchTowr can help your organization get ahead of AI-driven exploitation, request a demo.